Работа с AWS ASG(auto scaling group) и Terraform в Unix/Linux
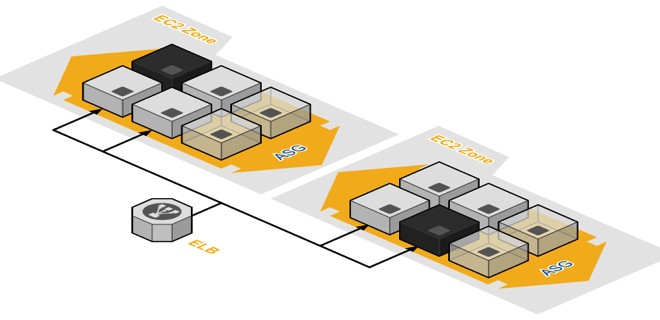
Auto Scaling позволяет поддерживать доступность приложений на неизменно высоком уровне и динамически масштабировать ресурсы Amazon EC2 как в сторону увеличения, так и в сторону уменьшения в автоматическом режиме, в зависимости от заданных условий. Auto Scaling можно использовать для управления группой инстансов Amazon EC2, чтобы поддерживать работоспособность и доступность группы и гарантировать, что в любой момент времени используется необходимое количество инстансов Amazon EC2. Можно также использовать Auto Scaling для динамического масштабирования инстансов EC2, чтобы автоматически увеличивать количество инстансов Amazon EC2 во время пиковых нагрузок для поддержания производительности и снижать объем используемых ресурсов в периоды затишья для сокращения затрат. Auto Scaling хорошо подходит как для приложений со стабильными схемами нагрузки, так и для приложений, уровень использования которых изменяется ежечасно, ежедневно или еженедельно. Помимо Auto Scaling для Amazon EC2 можно использовать возможность Application Auto Scaling для автоматического масштабирования ресурсов других сервисов AWS, включая Amazon ECS, группы спотовых инстансов Amazon EC2, кластеры Amazon EMR, группы инстансов AppStream 2.0 и Amazon DynamoDB.
Установка terraform в Unix/Linux
Установка крайне примитивная и я описал как это можно сделать тут:
Установка terraform в Unix/Linux
Так же, в данной статье, я создал скрипт для автоматической установки данного ПО. Он был протестирован на CentOS 6/7, Debian 8 и на Mac OS X. Все работает должным образом!
Чтобы получить помощь по использованию команд, выполните:
$ terraform
Usage: terraform [--version] [--help] <command> [args]
The available commands for execution are listed below.
The most common, useful commands are shown first, followed by
less common or more advanced commands. If you're just getting
started with Terraform, stick with the common commands. For the
other commands, please read the help and docs before usage.
Common commands:
apply Builds or changes infrastructure
console Interactive console for Terraform interpolations
destroy Destroy Terraform-managed infrastructure
env Workspace management
fmt Rewrites config files to canonical format
get Download and install modules for the configuration
graph Create a visual graph of Terraform resources
import Import existing infrastructure into Terraform
init Initialize a Terraform working directory
output Read an output from a state file
plan Generate and show an execution plan
providers Prints a tree of the providers used in the configuration
push Upload this Terraform module to Atlas to run
refresh Update local state file against real resources
show Inspect Terraform state or plan
taint Manually mark a resource for recreation
untaint Manually unmark a resource as tainted
validate Validates the Terraform files
version Prints the Terraform version
workspace Workspace management
All other commands:
debug Debug output management (experimental)
force-unlock Manually unlock the terraform state
state Advanced state management
Приступим к использованию!
Работа с AWS ASG(auto scaling group) и Terraform в Unix/Linux
У меня есть папка terraform, в ней у меня будут лежать провайдеры с которыми я буду работать. Т.к в этом примере я буду использовать AWS, то создам данную папку и перейду в нее. Далее, в этой папке, стоит создать:
$ mkdir examples modules
В папке examples, я буду хранить так званые «плейбуки» для разварачивания различных служб, например — zabbix-server, grafana, web-серверы и так далее. В modules директории, я буду хранить все необходимые модули.
Начнем писать модуль, но для этой задачи, я создам папку:
$ mkdir modules/asg
Переходим в нее:
$ cd modules/asg
Открываем файл:
$ vim asg.tf
В данный файл, вставляем:
#---------------------------------------------------
# Create AWS ASG
#---------------------------------------------------
resource "aws_autoscaling_group" "asg" {
count = "${var.create_asg}"
launch_configuration = "${var.create_lc ? element(aws_launch_configuration.lc.*.name, 0) : var.launch_configuration}"
#name = "${var.name}-asg-${var.environment}"
name_prefix = "${var.name}-asg-"
#Have got issue with availability_zones usage. So, I skip this parameter.
#availability_zones = ["${split(",", (lookup(var.availability_zones, var.region)))}"] #["us-east-1a", "us-east-1b"]
max_size = "${var.asg_max_size}"
min_size = "${var.asg_min_size}"
vpc_zone_identifier = ["${var.vpc_zone_identifier}"]
desired_capacity = "${var.desired_capacity}"
health_check_grace_period = "${var.health_check_grace_period}"
health_check_type = "${var.health_check_type}"
load_balancers = ["${var.load_balancers}"]
min_elb_capacity = "${var.min_elb_capacity}"
wait_for_elb_capacity = "${var.wait_for_elb_capacity}"
target_group_arns = ["${var.target_group_arns}"]
default_cooldown = "${var.default_cooldown}"
force_delete = "${var.force_delete}"
termination_policies = "${var.termination_policies}"
suspended_processes = "${var.suspended_processes}"
placement_group = "${var.placement_group}"
enabled_metrics = ["${var.enabled_metrics}"]
metrics_granularity = "${var.metrics_granularity}"
wait_for_capacity_timeout = "${var.wait_for_capacity_timeout}"
protect_from_scale_in = "${var.protect_from_scale_in}"
tags = [
{
key = "Name"
value = "${data.template_file.instances_index.rendered}"
propagate_at_launch = true
},
{
key = "Environment"
value = "${var.environment}"
propagate_at_launch = true
},
{
key = "Orchestration"
value = "${var.orchestration}"
propagate_at_launch = true
},
{
key = "Createdby"
value = "${var.createdby}"
propagate_at_launch = true
},
]
depends_on = ["aws_launch_configuration.lc"]
}
#---------------------------------------------------
# Data for ASG
#---------------------------------------------------
data "template_file" "instances_index" {
count = "${var.asg_max_size}"
template = "${lower(var.name)}-${lower(var.environment)}-${count.index+1}"
}
#---------------------------------------------------
# Define SSH key pair for our instances
#---------------------------------------------------
resource "aws_key_pair" "key_pair" {
key_name = "${lower(var.name)}-key_pair-${lower(var.environment)}"
public_key = "${file("${var.key_path}")}"
}
#---------------------------------------------------
# Launch AWS configuration
#---------------------------------------------------
resource "aws_launch_configuration" "lc" {
count = "${var.create_lc}"
#name = "${var.name}-lc-${var.environment}"
name_prefix = "${var.name}-lc-"
image_id = "${lookup(var.ami, var.region)}"
instance_type = "${var.ec2_instance_type}"
security_groups = ["${var.security_groups}"]
iam_instance_profile = "${var.iam_instance_profile}"
key_name = "${aws_key_pair.key_pair.id}"
user_data = "${var.user_data}"
associate_public_ip_address = "${var.enable_associate_public_ip_address}"
enable_monitoring = "${var.monitoring}"
placement_tenancy = "${var.placement_tenancy}"
#placement_tenancy does not work with spot_price
#spot_price = "${var.spot_price}"
ebs_optimized = "${var.ebs_optimized}"
ebs_block_device = "${var.ebs_block_device}"
ephemeral_block_device = "${var.ephemeral_block_device}"
root_block_device = "${var.root_block_device}"
lifecycle {
create_before_destroy = "true" #"${var.enable_create_before_destroy}"
}
depends_on = ["aws_key_pair.key_pair"]
}
#---------------------------------------------------
# Add autoscaling policy rules
#---------------------------------------------------
resource "aws_autoscaling_policy" "scale_up" {
count = "${var.enable_autoscaling_schedule ? 1 : 0}"
name = "${var.name}-asg_policy-${var.environment}-scale_up"
scaling_adjustment = "${var.asg_size_scale}"
adjustment_type = "${var.adjustment_type}"
cooldown = "${var.default_cooldown}"
autoscaling_group_name = "${aws_autoscaling_group.asg.name}"
lifecycle {
create_before_destroy = true
}
depends_on = ["aws_autoscaling_group.asg"]
}
resource "aws_autoscaling_policy" "scale_down" {
count = "${var.enable_autoscaling_schedule ? 1 : 0}"
name = "${var.name}-asg_policy-${var.environment}-scale_down"
scaling_adjustment = "-${var.asg_size_scale}"
adjustment_type = "${var.adjustment_type}"
cooldown = "${var.default_cooldown}"
autoscaling_group_name = "${aws_autoscaling_group.asg.name}"
lifecycle {
create_before_destroy = true
}
depends_on = ["aws_autoscaling_group.asg"]
}
#---------------------------------------------------
# ASW ASG Scale-up/Scale-down
#---------------------------------------------------
resource "aws_autoscaling_schedule" "scale_out_during_business_hours" {
count = "${var.enable_autoscaling_schedule ? 1 : 0}"
scheduled_action_name = "scale-out-during-business-hours"
min_size = "${var.asg_min_size}"
max_size = "${var.asg_size_scale}"
desired_capacity = "${var.asg_size_scale}"
recurrence = "${var.asg_recurrence_scale_up}"
autoscaling_group_name = "${aws_autoscaling_group.asg.name}"
depends_on = ["aws_autoscaling_group.asg"]
}
resource "aws_autoscaling_schedule" "scale_in_at_night" {
count = "${var.enable_autoscaling_schedule ? 1 : 0}"
scheduled_action_name = "scale-in-at-night"
min_size = "${var.asg_min_size}"
max_size = "${var.asg_size_scale}"
desired_capacity = "${var.asg_min_size}"
recurrence = "${var.asg_recurrence_scale_down}"
autoscaling_group_name = "${aws_autoscaling_group.asg.name}"
depends_on = ["aws_autoscaling_group.asg"]
}
Открываем файл:
$ vim variables.tf
И прописываем:
#-----------------------------------------------------------
# Global or/and default variables
#-----------------------------------------------------------
variable "name" {
description = "Name to be used on all resources as prefix"
default = "TEST-ASG"
}
variable "region" {
description = "The region where to deploy this code (e.g. us-east-1)."
default = "us-east-1"
}
variable "environment" {
description = "Environment for service"
default = "STAGE"
}
variable "orchestration" {
description = "Type of orchestration"
default = "Terraform"
}
variable "createdby" {
description = "Created by"
default = "Vitaliy Natarov"
}
variable "create_lc" {
description = "Whether to create launch configuration"
default = true
}
variable "create_asg" {
description = "Whether to create autoscaling group"
default = true
}
# Launch configuration
variable "launch_configuration" {
description = "The name of the launch configuration to use (if it is created outside of this module)"
default = ""
}
variable "ec2_instance_type" {
description = "Type of instance t2.micro, m1.xlarge, c1.medium etc"
default = "t2.micro"
}
variable "iam_instance_profile" {
description = "The IAM Instance Profile to launch the instance with. Specified as the name of the Instance Profile."
default = ""
}
variable "key_path" {
description = "Key path to your RSA|DSA key"
default = "/Users/captain/.ssh/id_rsa.pub"
}
variable "security_groups" {
description = "A list of security group IDs to assign to the launch configuration"
type = "list"
}
variable "enable_associate_public_ip_address" {
description = "Enabling associate public ip address (Associate a public ip address with an instance in a VPC)"
default = false
}
variable "user_data" {
description = "The user data to provide when launching the instance"
default = ""
}
variable "monitoring" {
description = "If true, the launched EC2 instance will have detailed monitoring enabled"
default = false
}
variable "ebs_optimized" {
description = "If true, the launched EC2 instance will be EBS-optimized"
default = false
}
variable "root_block_device" {
description = "Customize details about the root block device of the instance. See Block Devices below for details"
default = []
}
variable "ebs_block_device" {
description = "Additional EBS block devices to attach to the instance"
default = []
}
variable "ephemeral_block_device" {
description = "Customize Ephemeral (also known as Instance Store) volumes on the instance"
default = []
}
variable "spot_price" {
description = "The price to use for reserving spot instances"
default = 0
}
variable "placement_tenancy" {
description = "The tenancy of the instance. Valid values are 'default' or 'dedicated'"
default = "default"
}
variable "availability_zones" {
description = "Availability zones for AWS ASG"
type = "map"
default = {
us-east-1 = "us-east-1b,us-east-1c,us-east-1d,us-east-1e"
us-east-2 = "us-east-2a,eu-east-2b,eu-east-2c"
us-west-1 = "us-west-1a,us-west-1c"
us-west-2 = "us-west-2a,us-west-2b,us-west-2c"
ca-central-1 = "ca-central-1a,ca-central-1b"
eu-west-1 = "eu-west-1a,eu-west-1b,eu-west-1c"
eu-west-2 = "eu-west-2a,eu-west-2b"
eu-central-1 = "eu-central-1a,eu-central-1b,eu-central-1c"
ap-south-1 = "ap-south-1a,ap-south-1b"
sa-east-1 = "sa-east-1a,sa-east-1c"
ap-northeast-1 = "ap-northeast-1a,ap-northeast-1c"
ap-southeast-1 = "ap-southeast-1a,ap-southeast-1b"
ap-southeast-2 = "ap-southeast-2a,ap-southeast-2b,ap-southeast-2c"
ap-northeast-1 = "ap-northeast-1a,ap-northeast-1c"
ap-northeast-2 = "ap-northeast-2a,ap-northeast-2c"
}
}
variable "ami" {
description = "I added only 3 regions to show the map feature but you can add all"
type = "map"
default = {
us-east-1 = "ami-46c1b650"
us-west-2 = "ami-46c1b632"
eu-west-1 = "ami-6e28b517"
}
}
variable "enable_create_before_destroy" {
description = "Create before destroy"
default = "true"
}
# Autoscaling group
variable "asg_max_size" {
description = "Max size of instances to making autoscaling"
default = "1"
}
variable "asg_size_scale" {
description = "Size of instances to making autoscaling(up/down)"
default = "1"
}
variable "asg_min_size" {
description = "Min size of instances to making autoscaling"
default = "1"
}
variable "adjustment_type" {
description = "Specifies whether the adjustment is an absolute number or a percentage of the current capacity. Valid values are ChangeInCapacity, ExactCapacity, and PercentChangeInCapacity."
default = "ChangeInCapacity"
}
variable "asg_recurrence_scale_up" {
description = " Cronjob time for scale-up"
default = "0 9 * * *"
}
variable "asg_recurrence_scale_down" {
description = " Cronjob time for scale-down"
default = "0 17 * * *"
}
variable "enable_autoscaling_schedule" {
description = "Enabling autoscaling schedule"
default = false
}
variable "desired_capacity" {
description = "Desired numbers of servers in ASG"
default = 1
}
variable "vpc_zone_identifier" {
description = "A list of subnet IDs to launch resources in"
type = "list"
}
variable "default_cooldown" {
description = "The amount of time, in seconds, after a scaling activity completes before another scaling activity can start"
default = 300
}
variable "health_check_grace_period" {
description = "Time (in seconds) after instance comes into service before checking health."
default = 300
}
variable "health_check_type" {
description = "Controls how health checking is done. Need to choose 'EC2' or 'ELB'"
default = "EC2"
}
variable "force_delete" {
description = "Allows deleting the autoscaling group without waiting for all instances in the pool to terminate."
default = "true"
}
variable "load_balancers" {
description = "A list of elastic load balancer names to add to the autoscaling group names"
default = []
}
variable "target_group_arns" {
description = "A list of aws_alb_target_group ARNs, for use with Application Load Balancing"
default = []
}
variable "termination_policies" {
description = "A list of policies to decide how the instances in the auto scale group should be terminated. The allowed values are OldestInstance, NewestInstance, OldestLaunchConfiguration, ClosestToNextInstanceHour, Default"
type = "list"
default = ["Default"]
}
variable "suspended_processes" {
description = "A list of processes to suspend for the AutoScaling Group. The allowed values are Launch, Terminate, HealthCheck, ReplaceUnhealthy, AZRebalance, AlarmNotification, ScheduledActions, AddToLoadBalancer. Note that if you suspend either the Launch or Terminate process types, it can prevent your autoscaling group from functioning properly."
default = []
}
variable "placement_group" {
description = "The name of the placement group into which you'll launch your instances, if any"
default = ""
}
variable "metrics_granularity" {
description = "The granularity to associate with the metrics to collect. The only valid value is 1Minute"
default = "1Minute"
}
variable "enabled_metrics" {
description = "A list of metrics to collect. The allowed values are GroupMinSize, GroupMaxSize, GroupDesiredCapacity, GroupInServiceInstances, GroupPendingInstances, GroupStandbyInstances, GroupTerminatingInstances, GroupTotalInstances"
type = "list"
default = [
"GroupMinSize",
"GroupMaxSize",
"GroupDesiredCapacity",
"GroupInServiceInstances",
"GroupPendingInstances",
"GroupStandbyInstances",
"GroupTerminatingInstances",
"GroupTotalInstances",
]
}
variable "wait_for_capacity_timeout" {
description = "A maximum duration that Terraform should wait for ASG instances to be healthy before timing out. (See also Waiting for Capacity below.) Setting this to '0' causes Terraform to skip all Capacity Waiting behavior."
default = "10m"
}
variable "min_elb_capacity" {
description = "Setting this causes Terraform to wait for this number of instances to show up healthy in the ELB only on creation. Updates will not wait on ELB instance number changes"
default = 0
}
variable "wait_for_elb_capacity" {
description = "Setting this will cause Terraform to wait for exactly this number of healthy instances in all attached load balancers on both create and update operations. Takes precedence over min_elb_capacity behavior."
default = false
}
variable "protect_from_scale_in" {
description = "Allows setting instance protection. The autoscaling group will not select instances with this setting for terminination during scale in events."
default = false
}
Собственно в этом файле храняться все переменные. Спасибо кэп!
Открываем последний файл:
$ vim outputs.tf
и в него вставить нужно следующие строки:
# Launch configuration
output "this_launch_configuration_id" {
description = "The ID of the launch configuration"
value = "${var.launch_configuration == "" && var.create_lc ? element(concat(aws_launch_configuration.lc.*.id, list("")), 0) : var.launch_configuration}"
}
output "this_launch_configuration_name" {
description = "The name of the launch configuration"
value = "${var.launch_configuration == "" && var.create_lc ? element(concat(aws_launch_configuration.lc.*.name, list("")), 0) : ""}"
}
# Autoscaling group
output "this_autoscaling_group_id" {
description = "The autoscaling group id"
value = "${element(concat(aws_autoscaling_group.asg.*.id, list("")), 0)}"
}
output "this_autoscaling_group_name" {
description = "The autoscaling group name"
value = "${element(concat(aws_autoscaling_group.asg.*.name, list("")), 0)}"
}
output "this_autoscaling_group_arn" {
description = "The ARN for this AutoScaling Group"
value = "${element(concat(aws_autoscaling_group.asg.*.arn, list("")), 0)}"
}
output "this_autoscaling_group_min_size" {
description = "The minimum size of the autoscale group"
value = "${element(concat(aws_autoscaling_group.asg.*.min_size, list("")), 0)}"
}
output "this_autoscaling_group_max_size" {
description = "The maximum size of the autoscale group"
value = "${element(concat(aws_autoscaling_group.asg.*.max_size, list("")), 0)}"
}
output "this_autoscaling_group_desired_capacity" {
description = "The number of Amazon EC2 instances that should be running in the group"
value = "${element(concat(aws_autoscaling_group.asg.*.desired_capacity, list("")), 0)}"
}
output "this_autoscaling_group_default_cooldown" {
description = "Time between a scaling activity and the succeeding scaling activity"
value = "${element(concat(aws_autoscaling_group.asg.*.default_cooldown, list("")), 0)}"
}
output "this_autoscaling_group_health_check_grace_period" {
description = "Time after instance comes into service before checking health"
value = "${element(concat(aws_autoscaling_group.asg.*.health_check_grace_period, list("")), 0)}"
}
output "this_autoscaling_group_health_check_type" {
description = "EC2 or ELB. Controls how health checking is done"
value = "${element(concat(aws_autoscaling_group.asg.*.health_check_type, list("")), 0)}"
}
Переходим теперь в папку aws/examples и создадим еще одну папку для проверки написанного чуда:
$ mkdir asg && cd $_
Внутри созданной папки открываем файл:
$ vim main.tf
И вставим в него следующий код:
#
# MAINTAINER Vitaliy Natarov "vitaliy.natarov@yahoo.com"
#
terraform {
required_version = "> 0.9.0"
}
provider "aws" {
region = "us-east-1"
profile = "default"
# Make it faster by skipping something
#skip_get_ec2_platforms = true
#skip_metadata_api_check = true
#skip_region_validation = true
#skip_credentials_validation = true
#skip_requesting_account_id = true
}
module "iam" {
source = "../../modules/iam"
name = "TEST-AIM"
region = "us-east-1"
environment = "PROD"
aws_iam_role-principals = [
"ec2.amazonaws.com",
]
aws_iam_policy-actions = [
"cloudwatch:GetMetricStatistics",
"logs:DescribeLogStreams",
"logs:GetLogEvents",
"elasticache:Describe*",
"rds:Describe*",
"rds:ListTagsForResource",
"ec2:DescribeAccountAttributes",
"ec2:DescribeAvailabilityZones",
"ec2:DescribeSecurityGroups",
"ec2:DescribeVpcs",
"ec2:Owner",
]
}
module "vpc" {
source = "../../modules/vpc"
name = "TEST-VPC"
environment = "PROD"
# VPC
instance_tenancy = "default"
enable_dns_support = "true"
enable_dns_hostnames = "true"
assign_generated_ipv6_cidr_block = "false"
enable_classiclink = "false"
vpc_cidr = "172.31.0.0/16"
private_subnet_cidrs = ["172.31.64.0/20"]
public_subnet_cidrs = ["172.31.0.0/20"]
availability_zones = ["us-east-1a", "us-east-1b"]
enable_all_egress_ports = "true"
allowed_ports = ["9300", "3306", "80", "443"]
map_public_ip_on_launch = "true"
#Internet-GateWay
enable_internet_gateway = "true"
#NAT
enable_nat_gateway = "false"
single_nat_gateway = "true"
#VPN
enable_vpn_gateway = "false"
#DHCP
enable_dhcp_options = "false"
# EIP
enable_eip = "false"
}
module "elb" {
source = "../../modules/elb"
name = "TEST-ELB"
region = "us-east-1"
environment = "PROD"
security_groups = ["${module.vpc.security_group_id}"]
# Need to choose subnets or availability_zones. The subnets has been chosen.
subnets = ["${element(module.vpc.vpc-publicsubnet-ids, 0)}"]
#access_logs = [
# {
# bucket = "my-access-logs-bucket"
# bucket_prefix = "bar"
# interval = 60
# },
#]
listener = [
{
instance_port = "80"
instance_protocol = "HTTP"
lb_port = "80"
lb_protocol = "HTTP"
},
# {
# instance_port = 443
# instance_protocol = "https"
# lb_port = 443
# lb_protocol = "https"
# ssl_certificate_id = "${var.elb_certificate}"
# },
]
health_check = [
{
target = "HTTP:80/"
interval = 30
healthy_threshold = 2
unhealthy_threshold = 2
timeout = 5
}
]
# You could use ONE health_check!
#health_check = [
# {
# target = "HTTP:443/"
# interval = 30
# healthy_threshold = 2
# unhealthy_threshold = 2
# timeout = 5
# }
#]
# Enable
enable_lb_cookie_stickiness_policy_http = true
# Enable
enable_app_cookie_stickiness_policy_http = "true"
}
module "asg" {
source = "../../modules/asg"
name = "TEST-ASG"
region = "us-east-1"
environment = "PROD"
security_groups = ["${module.vpc.security_group_id}"]
root_block_device = [
{
volume_size = "8"
volume_type = "gp2"
},
]
# Auto scaling group
#asg_name = "example-asg"
vpc_zone_identifier = ["${module.vpc.vpc-publicsubnet-ids}"]
health_check_type = "EC2"
asg_min_size = 0
asg_max_size = 1
desired_capacity = 1
wait_for_capacity_timeout = 0
load_balancers = ["${module.elb.elb_name}"]
#
enable_autoscaling_schedule = true
}
PS: Тут имеются вспомогательные модули. Я описывал работу тут:
Работа с AWS IAM и Terraform в Unix/Linux
Работа с AWS VPC и Terraform в Unix/Linux
Для общего развития, можно ознакомится еще с (Он тут не нужен):
Работа с AWS EC2 и Terraform в Unix/Linux
Работа с AWS RDS и Terraform в Unix/Linux
Работа с AWS S3 и Terraform в Unix/Linux
Работа с AWS Route53 и Terraform в Unix/Linux
Так же, можно использовать:
Работа с AWS ELB и Terraform в Unix/Linux
Все уже написано и готово к использованию. Ну что, начнем тестирование. В папке с вашим плейбуком, выполняем:
$ terraform init
Этим действием я инициализирую проект. Затем, подтягиваю модуль:
$ terraform get
PS: Для обновление изменений в самом модуле, можно выполнять:
$ terraform get -update
Запускем прогон:
$ terraform plan
Мне вывело что все у меня хорошо и можно запускать деплой:
$ terraform apply
Как видно с вывода, — все прошло гладко! Чтобы удалить созданное творение, можно выполнить:
$ terraform destroy
У меня уже имеются наработки на github, вот аккаунт:
$ git clone https://github.com/SebastianUA/terraform.git
Вот и все на этом. Данная статья «Работа с AWS ELB и Terraform в Unix/Linux» завершена.